CyberCrime Articles
Archives
Microsoft Scam
The desktop typically looks like this after a scammer has gained access to the victim's computer.
________________________________________________
--------------------
--------------------
________________________________________________
Note from Richard Cunha of COMPTU (February, 2018, email to clients)
--------------------
Note from Richard Cunha of COMPTU (March, 2018, phone safety tips)
________________________________________________
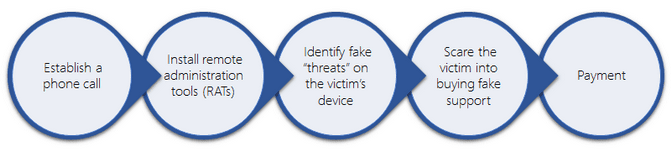
The above image is how it is played out and is typcally done in this order
________________________________________________
--------------------
--------------------
--------------------
--------------------
Watch the "Inside Man" and sign up for all 12 episodes

--------------------
Latest articles of which you need to be aware

- Global threat activity / Countries or regions with the most malware encounters in the last 30 days
- Top five tips for improving your online security
- UK police forces launch nationwide crackdown on Webstresser users
- Hackers breached Airbus’ IT systems; stole personal data of employees
- Chrome browser will soon start flagging domain-spoofing URLs
- Security Exploit in iOS 12.1.2 on iPhone XS Discovered
- Two-Fifths of Firms Have Suffered "BPC" Attacks
- There is an Expected 60% Increase in Cybercrime
- Preparing for Tomorrow's Threats Today
- Eastern European banks lose tens of millions of dollars in Hollywood-style hacks
- Humble Bundle breach could be first step in wider attack
- Sennheiser Headset Software Could Allow Man-in-the-Middle SSL Attacks
- Moscow’s cable car service shuts down in 2 days after ransomware attack
- Tech Support Scams Using Multiple Obfuscation Methods to Bypass Detection
- Ransomware Attack Impacts EHR of Rhode Island Provider
- ATM attackers strike again: Are you at risk?
- FBI swats down massive, botnet-fueled ad fraud operation
- Hacker adds malicious bitcoin-stealing code to popular JavaScript library
- Half of all Phishing Sites Now Have the Padlock
- Hackers target Drupal servers chaining several flaws, including Drupalgeddon2 and DirtyCOW
- Will good prevail over bad as bots battle for the internet?
- Nordstrom data breach exposes employee information
- Target and other high profile Twitter accounts exploited for cryptocurrency scams
- SSNs, Tax Data Exposed in Healthcare.gov Health Data Breach
- Apple and Samsung fined millions for intentionally slowing down old smartphones
- Unpatched MS Word Flaw Could Allow Hackers to Infect Your Computer
- Microsoft has been serving a malware-filled Chrome link through Bing
- Hackers Breached into System that Interacts with HealthCare.gov
- Email Still Poses a Cyber-Threat, but There is Hope
- A powerful, easy-to-use password stealing program known as #AgentTesla has been infecting computers since 2014, but recently this malware strain has seen a surge in popularity
- Mega cybersecurity coalition courts Walmart, Microsoft for next-generation defense
- How to make elections secure in the age of digital operatives
- UK cyber-centre thwarts hostile hackers
- Swedish court tells ISP to block The Pirate Bay in the country
- Tumblr Patches A Flaw That Could Have Exposed Users’ Account Info
- Authorities search & seize properties of GTA V’s “Infamous” cheat developers
- Cybersecurity job gap grows to 3 million, report
- The Week in Ransomware - October 12th 2018 - NotPetya, GandCrab, and More
- Cryptomining attacks against Apple devices increase sharply
- Facebook Clarifies Extent of Data Breach - 30 Million Affected; 14 Million Had Extensive Information Exposed
- Ad Clicker Hiding as Google Photos App Found in Microsoft Store
- Modern-day bank robbing: How hackers are becoming public enemy No. 1
- IoT security: Follow these rules to protect your users from hackers, gadget makers told
- New Technique Recycles Exploit Chain to Keep Antivirus Silent
- BEC attack scams Texas school district out of $600,000
- Aetna Hit With More Penalties for Two Breaches
- Fake Adobe updates installing cryptomining malware while updating Flash
- New GreyEnergy Malware Targets ICS, Tied with BlackEnergy and TeleBots
- Pentagon data breach puts personal details of 30,000 staff at risk
- US Voter Records for Sale on Hacker Forum
- Major Browsers to Kill TLS 1.0, 1.1
- Google to Encrypt Android Cloud Backups With Your Lock Screen Password
- Feds Investigate After Hackers Attack Water Utility
- Facebook Offers Details on ‘View As’ Breach, Revises Numbers
- Russia-Linked Hackers Target Diplomatic Entities in Central Asia
- Identity spoofing is the most prevalent attack vector for the gaming and gambling industry
- Bug in Newly Released iOS 12.0.1 Gives Access To Your Photos
- Octopus malware wraps tentacles around former Telegram users in Central Asia
- LibSSH Flaw Allows Hackers to Take Over Servers Without Password
- GrandCrab Ransomware Spreads Using Multiple Known Vulnerabilities

